ZetaChain’s $334K Meltdown: Did Ignoring This One Bug Report Seal Their Fate?
Ever wonder how a $334K crypto exploit could’ve been totally avoidable just by paying attention to a few bug reports? Well, ZetaChain’s recent fiasco is a textbook case of getting burned by ignoring the warning signs. They openly confessed that the vulnerability the attacker exploited had already been flagged in their bug bounty program—but was brushed off as “by design.” That’s like locking your door, seeing the lock jammed, and then shrugging it off until the thief walks right in. Moving forward, they’re promising to take bug reports more seriously, especially those complex chained attack vectors that — frankly — should never be underestimated. Plus, while it was protocol-controlled wallets that took the hit (phew, no user funds lost!), this incident underscores a much bigger problem that’s been bleeding the crypto space dry. With April hacking losses topping $600 million — the worst month yet in 2026 — the message is clear: proactive threat detection isn’t optional anymore. And as if hackers weren’t scary enough, now we’re facing AI-powered cyber threats with models like Anthropic’s Mythos and OpenAI’s GPT-5.5-Cyber lurking in the shadows, possibly turning up the heat on security risks even more. The big question is: Are we ready to step up our game before the next inevitable hit lands? Otherwise, mass crypto adoption might just stay a pipe dream. LEARN MORE
The ZetaChain’s $334K exploit was preventable if the team had taken earlier bug reports seriously.
In the post-mortem report, the team admitted that the gateway vulnerability leveraged by the attacker had been disclosed in a bug bounty program, but they dismissed it.
Prior to the exploit, the vulnerability class had been reported through our bug bounty program. Initial reports were dismissed as the arbitrary call behavior was considered by design.
Going forward, the project added, it will review all bug bounty submissions to ensure “reports involving chained attack vectors receive appropriate severity assessment.”
That said, the project clarified that protocol-controlled wallets were the ones drained of $334K, adding that no user funds were lost.
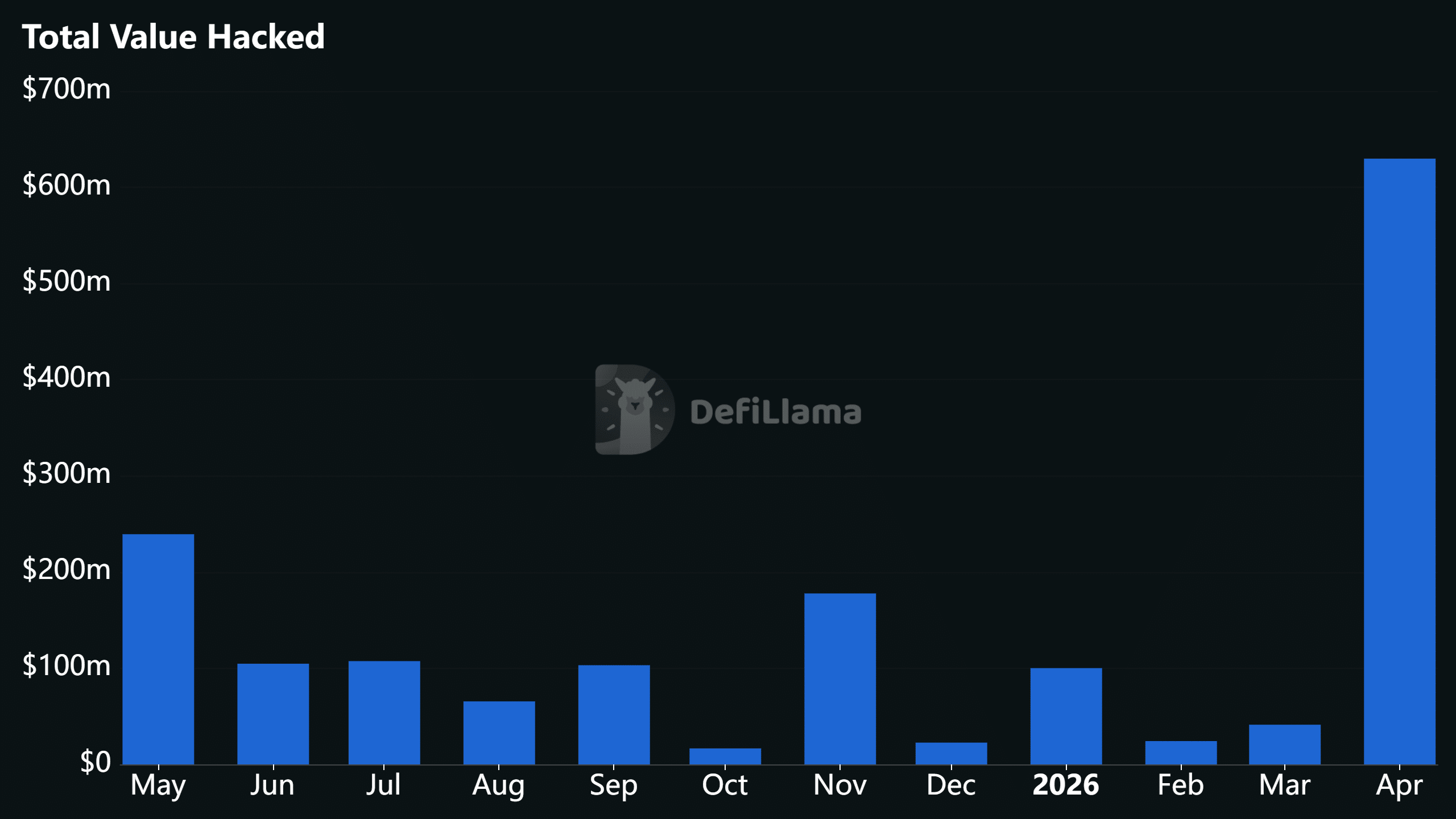
April crypto hack losses top $600M
In April, the losses from the rising crypto hacks hit $629 million, according to data tracked by DeFiLlama. This was the highest level of monthly losses so far in 2026.
In fact, even when zoomed out on a year-on-year (YoY) basis, it was still the largest loss.

This week alone, Aftermath Perps lost $1.14 million while Sweat Foundation suffered a $3.5M breach. ZetaChain, Judao, Scallop Lend, Syndicate, and Quant also suffered exploits ranging between $150K to $413K each.
Last week, Volo Vault, Purrlend, and Giddy also added to the growing list of victims. Perhaps the most notable victim in April is the Kelp DAO’s $293 million exploit, which triggered massive outflows across the DeFi ecosystem.
Yet, some of these exploits are preventable, especially with strong bug bounty programs. In the ZetaChain case, for example, there was a prior bug submission, which was ignored.
At the same time, the attacker did some tests before the exploit, which could be flagged by strong threat monitoring.
Now the industry will contend with another powerful threat actor: AI-powered models. Cybersecurity models with offensive capabilities like Anthropic’s Claude-powered Mythos and recently announced OpenAI’s GPT-5.5-Cyber are yet to be made public.
The reported offensive capability of these models should be a warning sign for the entire industry to take security measures more seriously or forget about mass adoption.
Final Summary
- ZetaChain admitted its $334K exploit was from a bug that was previously reported but wasn’t acted on.
- Losses linked to DeFi hacks in April have now crossed $600M, underscoring the need for proactive threat detection.

















Post Comment