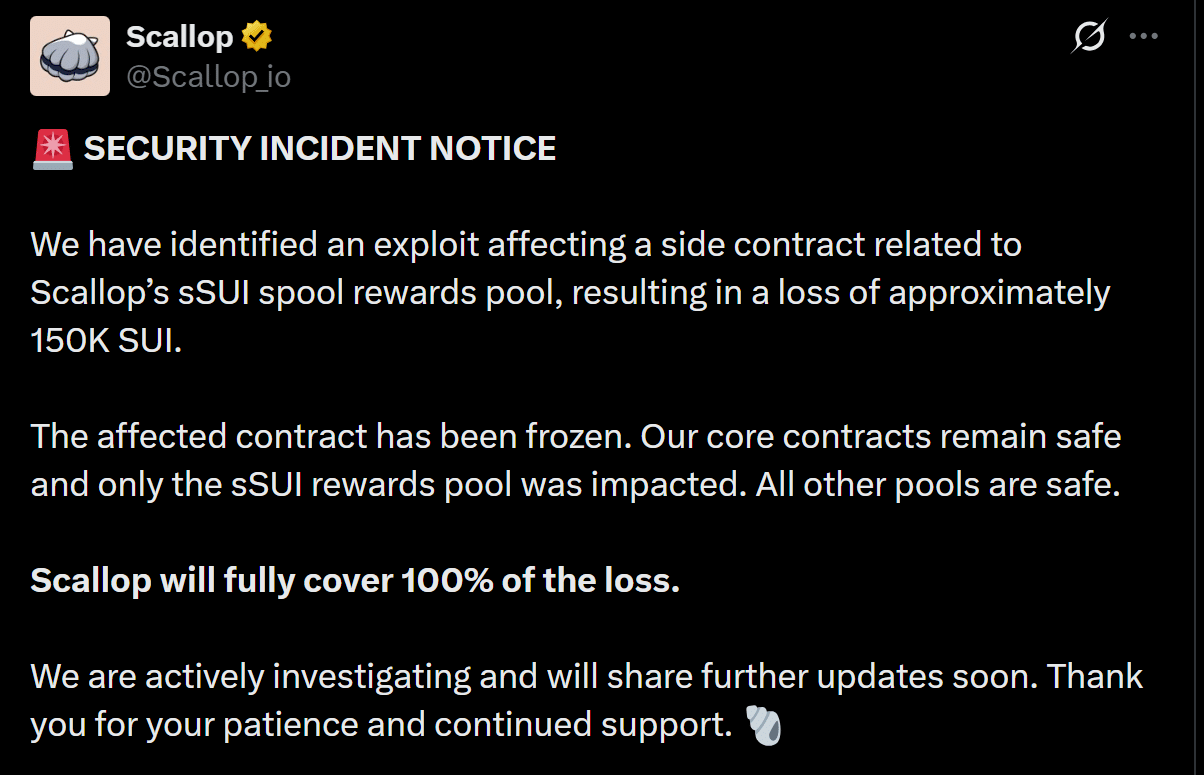
Scallop’s $150K SUI Heist: Is Core Liquidity the Real Casualty Investors Aren’t Talking About?
Ever wonder how a tiny crack in the side wall of a fortress can cause the whole place to tremble — or not? That’s exactly what happened with Scallop’s Sui [SUI] rewards pool recently. A slick exploit swooped in, draining a hefty 150,000 SUI, yet, surprisingly, the damage was squeezed into a narrow corner of the contract maze. Talk about laser-focused risk! The real kicker? It wasn’t the core system that got tapped, but a peripheral module playing a dangerous game of hide-and-seek with vulnerabilities. Now, here’s the million-dollar question — how often do we overlook these backdoors in our digital empires until someone else finds the keys first? Scallop’s quick freeze of the affected contract not only slammed the brakes on further losses but also showcased the power of a modular design in isolating shockwaves — saving the day and the deeper pockets of the protocol. There’s a lesson buried here about the unseen perils lurking beyond the well-audited core, and the fine line between trust and caution in the fast-evolving crypto space. Intrigued? Let’s dive in. LEARN MORE.
A security incident disrupted Scallop’s Sui [SUI] rewards pool recently. Fortunately, however, the damage was contained within a narrow contract layer. The exploit drained about 150K SUI, which pointed to a vulnerability in a side module rather than core infrastructure.
As this unfolded, the team froze the affected contract, limiting further losses and stabilizing user exposure. Core pools remained intact, which underlined how the protocol’s modular design isolated risk effectively. This response reduced the chance of broader liquidity shock across the ecosystem too.

More importantly, the event highlighted how peripheral contracts can introduce hidden risks. Scallop’s decision to cover 100% of losses helped restore confidence, while ongoing caution may influence short-term user activity and trust dynamics.
Old contract bug led to 150K SUI drain
The exploit unfolded through an overlooked contract path, showing the attacker understood exactly where to strike. The transaction involved about 150,098 SUI flowing to a single account, confirming the pool was drained.
This happened because an old V2 contract did not set the user’s last_index when staking. As a result, the system calculated rewards from the very beginning rather than from when staking started.

As the spool index had grown to about 1.19 billion, the attacker’s 136K sSUI stake multiplied instantly. This inflated rewards to about 150k SUI, which then flowed to a single wallet.
While core contracts stayed safe, this event was evidence of how forgotten code paths can create hidden risks, affecting trust and short-term user confidence.
Stability after exploit as user confidence holds
Following the exploit, Scallop restored operations, signaling a controlled recovery rather than systemic failure. Core contracts resumed as the issue remained isolated to a deprecated rewards module.

This containment reassured users, especially as deposits stayed safe and withdrawals continued normally. As a result, the TVL held near $22.37 million – A sign of no immediate panic-driven outflows. This stability suggested that users recognized the limited scope of the breach.
However, this response also highlighted a deeper issue, one where peripheral modules expand the attack surface beyond audited core logic. While confidence is holding for now, sustained trust will depend on continued stability in flows. If TVL remains steady or grows, confidence will strengthen, while delayed outflows could still emerge as users reassess protocol risk.

















Post Comment